- Nginx Generate Key From Crt Pdf
- Nginx Generate Key From Crt File
- Nginx Generate Key From Crt Tool
- Nginx Generate Key From Crt Download
- Nginx Generate Key From Crt Mac
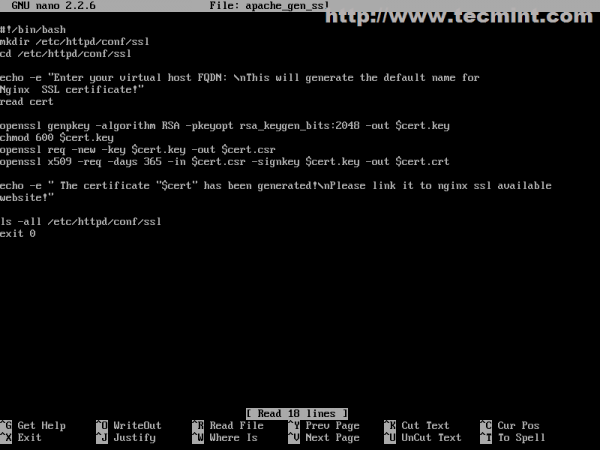
Apr 10, 2012 Create self-signed SSL certificate for Nginx. GitHub Gist: instantly share code, notes, and snippets. Installing NGINX Community Modules. For a community dynamic module to work with NGINX Plus, it must be compiled alongside the corresponding NGINX Open Source version. In this article I’m going to show you the commands you need to convert your.PFX Certificate file to a seperate certificate and keyfile. This article can come in handy when you need to import your certificates on devices like Cisco routers/loadbalancers etc. Where you probably need to import the certificates and keyfiles in plain text (unencrypted). We need a directory to store our certificates. Since the secrecy of this key is essential for security, we will lock down the permissions to prevent unauthorized access: mkdir /etc/nginx/ssl chmod 700 /etc/nginx/ssl. Create a self-signed key and certificate pair with.
Create a CSR using OpenSSL & install your SSL certificate on your Apache server
Use the instructions on this page to use OpenSSL to create your certificate signing request (CSR) and then to install your SSL certificate on your Apache server.
Restart Note: After you've installed your SSL/TLS certificate and configured the server to use it, you must restart your Apache instance.
For Ubuntu instructions, see Ubuntu Server with Apache2: Create CSR & Install SSL Certificate (OpenSSL). For other OS/platform instructions, see Create a CSR (Certificate Signing Request).
You can use these instructions to create OpenSSL CSRs and install all types of DigiCert SSL certificates on your Apache server: Standard SSL, EV SSL, Multi-Domain SSL, EV Multi-Domain SSL, and Wildcard SSL.
To create your certificate signing request (CSR), see Apache: Creating Your CSR with OpenSSL.
Para un tutorial en español visite la página Apache Crear CSR.
To install your SSL certificate, see Apache: Installing & Configuring Your SSL Certificate.
Visite nuestras instrucciones en español para Apache Instalar Certificado SSL.
I. Apache: Creating Your CSR with OpenSSL
Use the instructions in this section to create your own shell commands to generate your Apache CSR with OpenSSL.
Recommended: Save yourself some time. Use the DigiCert OpenSSL CSR Wizard to generate an OpenSSL command to create your Apache CSR. Just fill out the form, click Generate, and then paste your customized OpenSSL command into your terminal.
How to Generate a CSR for Apache Using OpenSSL
If you prefer to build your own shell commands to generate your Apache CSR, follow the instructions below.
Log in to your server via your terminal client (ssh).
Run Command
At the prompt, type the following command:
Note: Make sure to replace server with the name of your server.
Generate Files
You've now started the process for generating the following two files:
- Private-Key File: Used to generate the CSR and later to secure and verify connections using the certificate.
- Certificate Signing Request (CSR) file: Used to order your SSL certificate and later to encrypt messages that only its corresponding private key can decrypt.
When prompted for the Common Name (domain name), type the fully qualified domain (FQDN) for the site that you are going to secure.
Note: If you're generating an Apache CSR for a Wildcard certificate, make sure your common name starts with an asterisk (e.g., *.example.com).
When prompted, type your organizational information, beginning with your geographic information.
Note: You may have already set up default information.
Now, your OpenSSL .csr file is created.
Order Your SSL/TLS Certificate
Open the .csr file you created with a text editor.
Copy the text, including the -----BEGIN NEW CERTIFICATE REQUEST----- and -----END NEW CERTIFICATE REQUEST----- tags, and paste it in to the DigiCert order form.
Save Private Key
Save (back up) the generated .key file. You need it later to install your SSL certificate.
Install Certificate
After you've received your SSL certificate from DigiCert, you can install it on your server.
II. Apache: Installing & Configuring Your SSL Certificate
If you still need to create a certificate signing request (CSR) and order your certificate, see Apache: Creating Your CSR with OpenSSL.
After we've validated and issued your SSL certificate, you can install it on your Apache server (where the CSR was generated) and configure the server to use the certificate.
How to Install and Configure Your SSL Certificate on Your Apache Server
Copy the certificate files to your server.
Log in to your DigiCert account and download the intermediate (DigiCertCA.crt) and your primary certificate (your_domain_name.crt) files.
Copy these files, along with the .key file you generated when creating the CSR, to the directory on the server where you keep your certificate and key files.
Note: Make them readable by root only to increase security.
Find the Apache configuration file (httpd.conf) you need to edit.
The location and name of the configuration file can vary from server to server—especially if you're using a special interface to manage your server configuration.
Apache's main configuration file is typically named httpd.conf or apache2.conf. Possible locations for this file include /etc/httpd/ or /etc/apache2/. For a comprehensive listing of default installation layouts for Apache HTTPD on various operating systems and distributions, see Httpd Wiki - DistrosDefaultLayout.
Often, the SSL certificate configuration is located in a <VirtualHost> block in a different configuration file. The configuration files may be under a directory like /etc/httpd/vhosts.d/, /etc/httpd/sites/, or in a file called httpd-ssl.conf.
One way to locate the SSL Configuration on Linux distributions is to search using grep, as shown in the example below.
Run the following command:
Note: Make sure to replace /etc/httpd/ with the base directory for your Apache installation.
Identify the SSL <VirtualHost> block you need to configure.
If your site needs to be accessible through both secure (https) and non-secure (http) connections, you need a virtual host for each type of connection. Make a copy of the existing non-secure virtual host and configure it for SSL as described in step 4.
If your site only needs to be accessed securely, configure the existing virtual host for SSL as described in step 4.
Configure the <VirtualHost> block for the SSL-enabled site
Below is a very simple example of a virtual host configured for SSL. The parts listed in blue are the parts you must add for SSL configuration.
Make sure to adjust the file names to match your certificate files.
SSLCertificateFile is your DigiCert certificate file (e.g., your_domain_name.crt).
SSLCertificateKeyFile is the .key file generated when you created the CSR (e.g., your_private.key).
SSLCertificateChainFile is the DigiCert intermediate certificate file (e.g., DigiCertCA.crt)
Note: If the SSLCertificateChainFile directive does not work, try using the SSLCACertificateFile directive instead.
Test your Apache configuration file before restarting.
As a best practice, check your Apache configuration file for any errors before restarting Apache.
Caution: Apache won't start again if your configuration files have syntax errors.
Run the following command to test your configuration file (on some systems, it's apache2ctl):
Restart Apache.
You can use apachectl commands to stop and start Apache with SSL support.
Restart Notes:
If Apache doesn't restart with SSL support, try using apachectl startssl instead of apachectl start. If SSL support only loads with apachectl startssl, we recommend you adjust the apache startup configuration to include SSL support in the regular apachectl start command. Otherwise, your server may require to manually restart Apache using apachectl startssl in the event of a server reboot. This usually involves removing the <IfDefine SSL> and </IfDefine> tags that enclose your SSL configuration.
Congratulations! You've successfully installed your SSL certificate.
Testing Your SSL/TLS Certificate Installation
Browser Test
For best results, make sure to close your web browser first and then re-launch it.
Visit your site with the secure https URL (i.e., go to https://www.example.com not http://www.example.com).
Be sure to test your site with more than just Internet Explorer. IE downloads missing intermediate certificates; whereas, other browsers give an error if all the certificates in the certificate chain aren't installed properly.
DigiCert® SSL Installation Diagnostic Tool
If your site's publicly accessible, use our Server Certificate Tester to test your SSL/TLS certificate installation; it detects common installation problems.
Troubleshooting
If your web site's publicly accessible, our SSL Certificate Tester tool can help you diagnose common problems.
If you receive a 'not trusted' warning, view the certificate details to see if it's the certificate you expect. Check the Subject, Issuer, and Valid To fields.
If it's the certificate you expect and the SSL certificate is issued by DigiCert, then your SSLCertificateChainFile is not configured correctly.
If you don't see the certificate you expect, then you may have another SSL <VirtualHost> block before the one you recently configured.
Name based virtual hosts aren't possible with https unless you use the same certificate for all virtual hosts (e.g., a Wildcard or a Multi-Domain SSL certificate).
This is not an Apache limitation, but an SSL protocol limitation. Apache must send a certificate during the SSL handshake before it receives the HTTP request that contains the Host header. Therefore, Apache always sends the SSLCertificateFile from the first <VirtualHost> block that matches the IP and port of the request.
For help moving your certificates to additional servers or across server platforms, see our OpenSSL export instructions.
If you need to disable SSL version 2 compatibility in order to meet PCI Compliance requirements, add the following directive to your Apache configuration file:
Generate private key from public certificate. If the directive already exists, you may need to modify it to disable SSL version 2.
For instructions on how to fix common errors and for additional tips, see Troubleshooting Apache SSL Certificate Errors.
Apache Server Configuration
For information about Apache server configurations that can strengthen your SSL environment, see the following resources:
For Instructions on disabling the SSL v3 protocol, see Apache: Disabling the SSL v3 Protocol.
For information about enabling perfect forward secrecy, see Enabling Perfect Forward Secrecy.
SSL stands for 'Secure Sockets Layer', which is the standard security technology meant for creating an encrypted link between a Web server and a Web browser. This link ensures that all information passed between the server and browser remains private and secure. The main purpose of the SSL certificates is to assure the website security and encrypt data transferred between the client and the browser to prevent any theft of sensitive information such as credit card details, account numbers, and passwords etc.
A self-signed certificate is a certificate that is signed by the person creating it rather than a trusted certificate authority (CA). Most of the clients and organizations are tempted to use self-signed SSL Certificates instead of those issued and verified by a trusted Certificate Authority mainly because of the cost difference. But it still offers the same level of encryption to a limit.
In this article, I'll explain how to create a Self-Signed SSL certificate on an Ubuntu 18.04 server with Nginx Web server.
Pre-requisites
A well-configured server with root privileges and OpenSSL library. The OpenSSL library is required to generate your own certificate. Run the following command in your ubuntu server to see if you already have OpenSSL installed.
If the which command didn't return the binary, then we will need to install it using the command:
Creating the Self-Signed Certificate
SSL comprises of mainly two parts one is the private key and the other public certificate. The SSL key is kept private on the server restricted to the root user. It is actually used to encrypt content sent to clients. The public SSL certificate is shared with anyone requesting the content. It can be used to decrypt the content signed by the associated private SSL key. Here, I'm using this command to generate a self-signed certificate namely example.com.crt and a private key example.com.key( here I am using example.com.pem as the file name) using the OpenSSL tool.
Please see the details of each option below:
- req: This subcommand is used for creating a new X.509 cert. The 'X.509' is a public key infrastructure standard that SSL and TLS adhere to for its key and certificate management.
- -x509: This further modifies the previous subcommand by telling the utility that we want to make a self-signed certificate.
- -nodes: This is used to skip the passphrase option to secure our certificate.
- -days 365: This option sets the validity for the certificate in days. We are setting it for a year here.
- -newkey rsa:2048: This specifies that we want to generate a new RSA key with 2048 bits long along with the certificate.
- -keyout: This option tells OpenSSL where to place the generated private key file.
- -out: This option tells OpenSSL where to place the generated certificate.
During this command execution, it will prompt us to provide the domain/client details for generating a Certificate Signing Request (CSR). You can provide these details as required.
Now we have our newly generated self-signed certificate and private key is these locations namely: /etc/ssl/certs/example.com.pem and /etc/ssl/private/example.com.key. Next, we should create a strong Diffie-Hellman group, which is used in negotiating Perfect Forward Secrecy with clients. You can run this command to create one.
This might take some time to complete, but when it's done we will have a strong DH group at /etc/ssl/certs/dhparam.pem that we can use in our configuration.
Configuring Nginx to use Self-signed Certs
Before we begin, we need to make sure that Nginx web server is installed on our Ubuntu 18.04 server. If it's not installed then you can install it by using this simple command:
I've installed and enabled this service on my server.
Next. we can configure Nginx to use SSL. I'll explain that in three steps:
Nginx Generate Key From Crt Pdf
- Creating a snippet configuration with the generated SSL certificate details.
- Creating a snippet configuration for maintaining a Strong and Secure SSL settings overcoming possible SSL vulnerabilities.
- Updating the domain virtual host with the above snippet configurations to enable SSL
Step 1: Creating a snippet configuration with the SSL certificate details
Let's create a new snippet configuration file namely 'self-signed.conf' for pointing our generated Self-Signed Certificate details inside the Nginx snippet folder: /etc/nginx/snippets/ as below:
Here we need to specify our generated certificate path:/etc/ssl/certs/example.com.pem and Key path: /etc/ssl/private/example.com.key for the directive as mentioned above.
Step 2: Creating a snippet configuration for maintaining Strong and Secure SSL settings overcoming possible SSL vulnerabilities
Secondly, we need to maintain a fully functional and strong SSL server configuration protecting our server from all possible SSL vulnerabilities. I have configured my Nginx with a strong SSL cipher suite and enabled some advanced features to ensure the server security. All these parameters are included in the file: /etc/nginx/snippets/ssl-params.conf
You can get these Nginx Cipher recommendations in the Cipher list. These parameters will be used in future Nginx configurations for SSL. As you can see we have set the ssl_dhparam setting to point to the Diffie-Hellman file we generated earlier here. Since we are using a self-signed certificate, the SSL stapling will not be used. Hence, I have turned it off or else Nginx will simply output a warning like this nginx: [warn] 'ssl_stapling' ignored, issuer certificate not found for certificate. After making these changes you can save the configuration and exit.
Nginx Generate Key From Crt File
Step 3: Updating the domain virtual host with the above snippet configurations to enable SSL
We are ready with our required snippet configuration, now we can include those in our domain virtual host and enable SSL. Here in this article, I'm using the default Nginx configuration file located at /etc/nginx/sites-available/default. I've modified this file to enable SSL and fetch the generated Self-signed certificates. Please see the modified section below in this configuration:
Nginx Generate Key From Crt Tool
Now we can save these configurations and restart the Nginx service to make these changes effective.
Testing
This is our final step, where we can open up our browser and try to access our server IP at the URL >> https://Server_IP or Hostname. It will display a security warning since we are using a self-signed certificate, you can ignore that warning and click to confirm security to proceed further as shown in the snapshot.
Nginx Generate Key From Crt Download
Read Also :
Nginx Generate Key From Crt Mac
That's all! we've successfully configured Nginx with Self-signed certificate using strong encryption methods for secure client connections. I hope this article is useful to you! Please post your valuable comments and suggestions on this.
Most Viewed News
- ✔ Net Protector 2013 Key Generator
- ✔ Parallel Desktop 12 Key Generator
- ✔ Avast Pro Product Key Generator
- ✔ Linux Generate Ssh Authorized_keys
- ✔ Napoleon Total War Key Generator
- ✔ Microsoft Office 2007 Product Key Generator Free
- ✔ Key Generator For Origin Games
- ✔ Lotr Conquest Cd Key Generator
- ✔ Gta 4 Generate Serial Key
- ✔ Age Of Mythology Gold Product Key Generator